Introduction
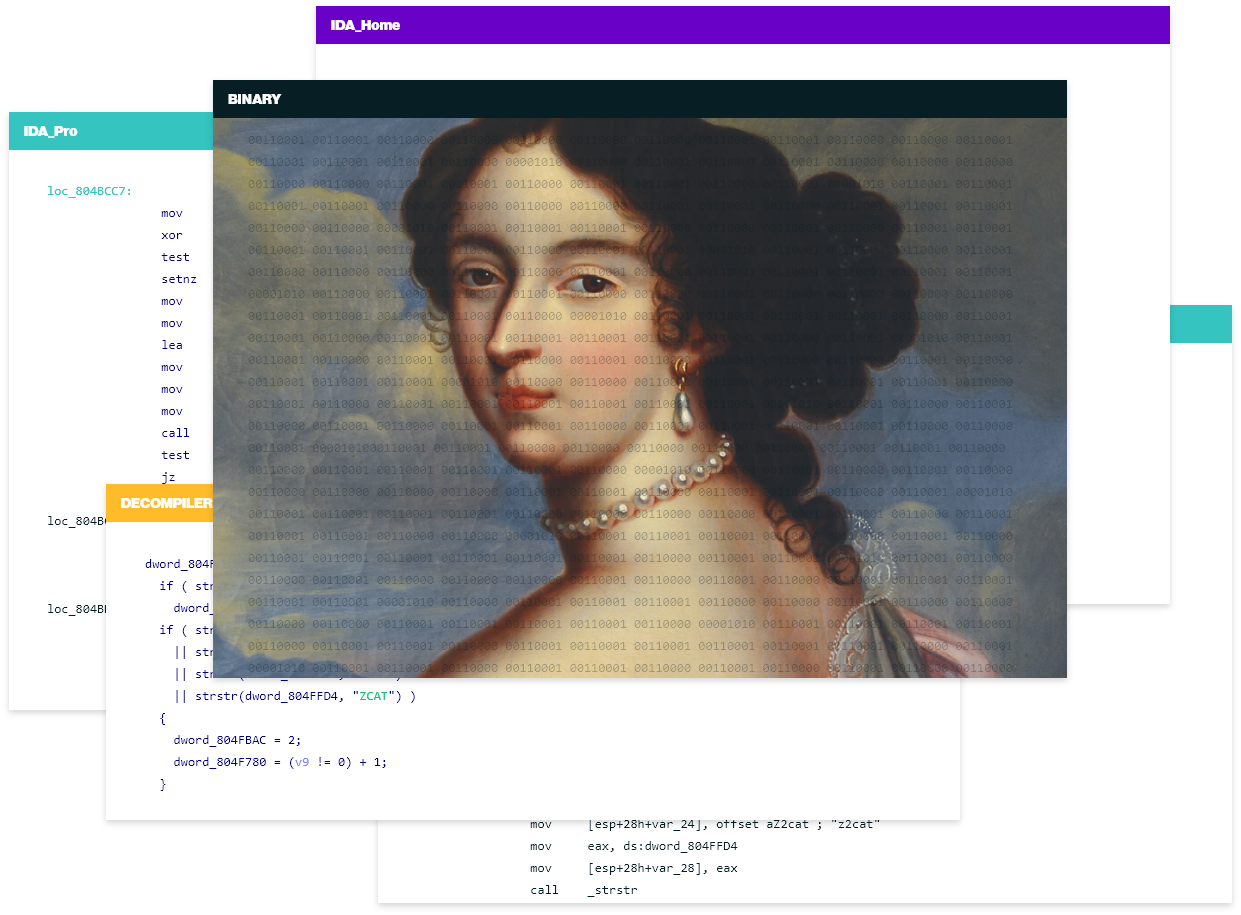
This training focuses on writing file format loaders and processor modules to extend IDA's functionality. Participants will perform prototyping using IDAPython and then write a full-blown implementation for a custom executable image format and processor architecture using the native C++ SDK.
Who would benefit from this course?
This course is an excellent option for experienced IDA Pro users aiming to enhance IDA through direct coding in IDA Python and the C++ SDK.
What you will learn
Students will learn how to build tools that help IDA recognize new file types, scripting using IDAPython, and then dive deep into programming with the IDA C++ SDK.
Prerequisites
Proficiency in IDA Pro, good knowledge of Python and C++
Location
Online
Date & Duration
Sept 18-19, 2024 10:00 UTC-4 (New York) - 1.5 days
About your trainer
Julian Kirsch has been using IDA Pro for his daily reverse engineering works for more than 15 years. At Hex-Rays, he works at the intersection of product, research, and development. He is an experienced instructor of reverse engineering classes, usually centered around deobfuscation and program analysis topics, with a focus on targets found in the real world. Julian graduated from TU Munich, where he has taught hands-on courses on reverse engineering and binary exploitation to students for six years. In his limited spare time, he organizes and participates in capture the flag contests alongside his teammates from hxp.
1.5 days
Date:Sept 18-19, 2024 10:00 UTC-4 (New York)
before Sept 17, 2024 15:00 UTC+2