Introduction
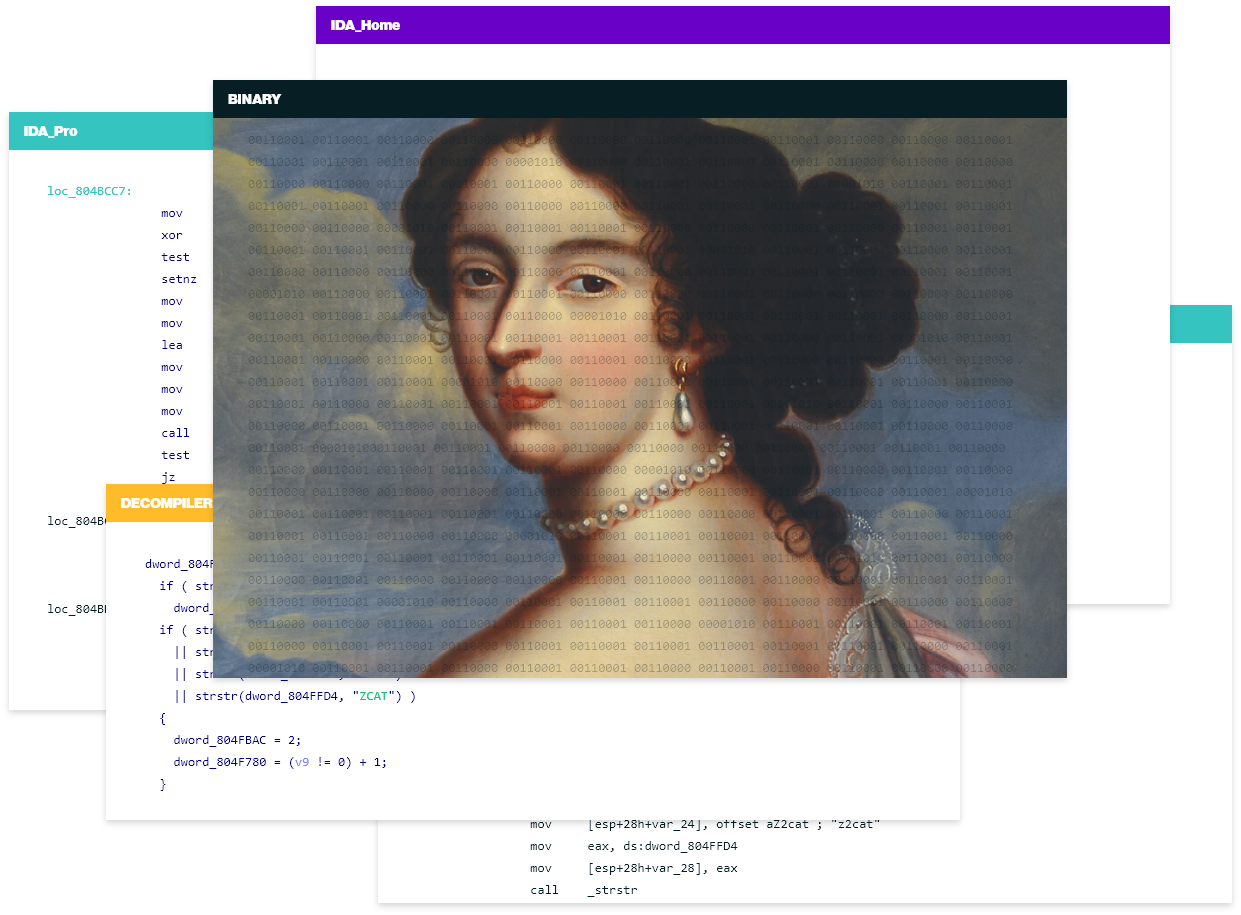
This one-day training is structured similarly to a standard analysis workflow. It starts with identifying and unpacking malware, including basic and sophisticated packers, while tackling common scenarios encountered in the process. Students will learn to work through defeating API hashing and string encryption within malware, leveraging plugins, and building their own custom tooling with IDA Python. From there, the session will conclude with gaining additional insights into analyzing further advanced malware techniques such as AV evasion, anti-analysis tactics, and advanced injection methods.
Who would benefit from this course?
This course is beneficial for experienced IDA users, malware analysts and security professionals who are willing to enhance their expertise in malware analysis using sophisticated methods and custom tool development with IDA Python.
What you will learn
Participants will develop proficiency in using IDA for malware analysis, gaining insights into countering advanced evasion and injection tactics used by modern malware. Students will learn to circumvent encryption and obfuscation techniques, and create powerful custom tools with IDA Python.
Prerequisites
Proficiency in IDA Pro, very good knowledge of Python
Location
Online
Date & Duration
Tue, September 24, 2024 10:00 UTC+2 (Paris) - 1 day
About your trainer
Daniel Bunce is a Security Researcher who specializes in Malware Reverse-Engineering. Initially starting off in the field interested in Offensive Security tactics, he used that knowledge to transition over to Reverse Engineering and Malware Analysis, where he now spends most of his time looking at Windows based E-Crime malware and working on tools for gathering further intelligence, such as developing automated unpackers, configuration extractors, and botnet communication emulators.
Course Content
To be published soon
1 day
Date: Tue, September 24, 2024 10:00 UTC+2 (Paris)
before Sept 23, 2024 15:00 UTC+2